AWS Security: IAM Best Practices for Engineers
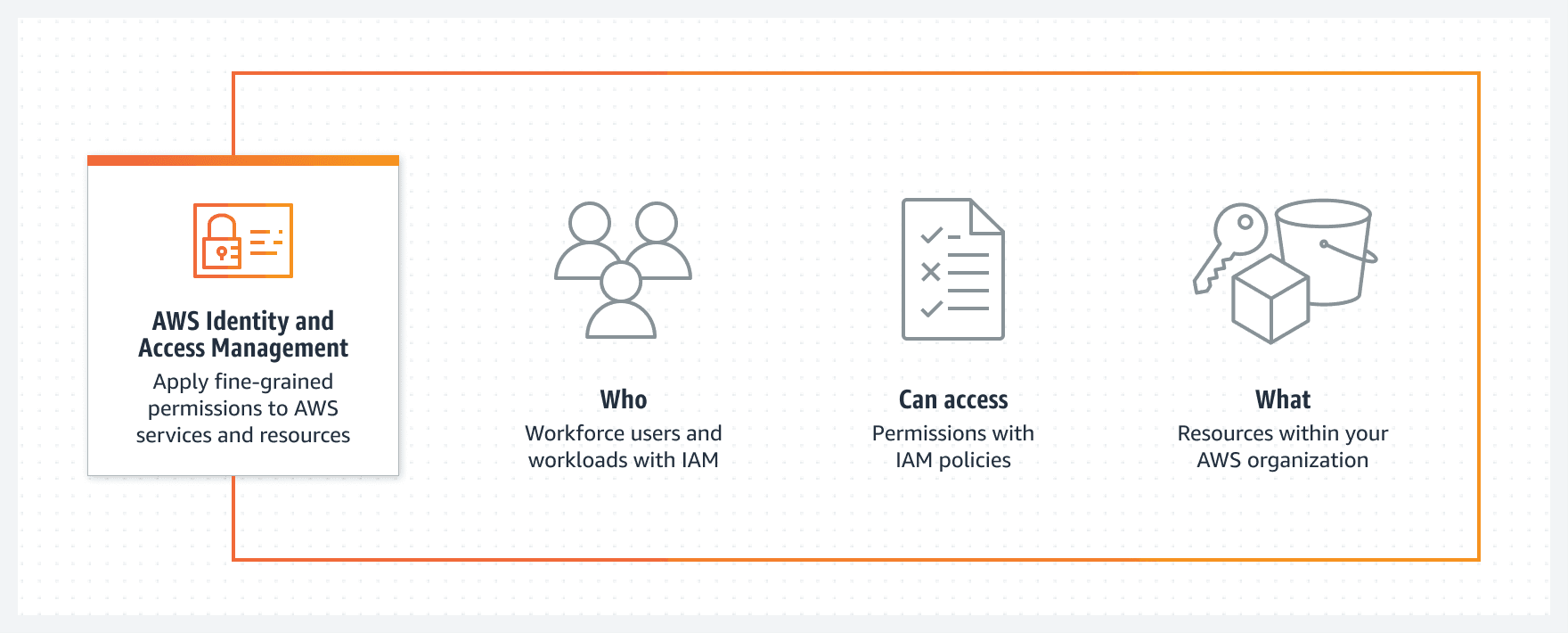
As an AWS cloud engineer, managing and securing your AWS resources is critical. One of the most important components in the AWS ecosystem for ensuring security is Identity and Access Management (IAM). IAM allows you to manage user access to resources, enabling you to implement fine-grained access control and protect sensitive data. In this article, we will discuss some of the best practices for using IAM to secure your AWS environment.
- Use the Principle of Least Privilege
When creating IAM policies, adhere to the principle of least privilege. This means granting users the minimum set of permissions required to perform their tasks. Overly permissive policies can expose your AWS resources to unnecessary risk, so regularly review and update your policies to ensure they align with the current needs of your organization.
- Implement Strong Password Policies
Enforce strong password policies for your IAM users. Require complex and lengthy passwords, and make sure they are changed regularly. This will help protect your AWS environment from unauthorized access due to weak or compromised passwords.
- Use Multi-Factor Authentication (MFA)
Enable Multi-Factor Authentication (MFA) for all IAM users, especially those with access to critical resources or elevated privileges. MFA adds an extra layer of security by requiring users to provide a unique authentication code generated by a separate device when signing in.
- Rotate Access Keys Regularly
Access keys are used for programmatic access to AWS services. To reduce the risk of unauthorized access, rotate access keys periodically and remove inactive keys. Additionally, avoid using access keys for root accounts, and instead create dedicated IAM users with the necessary permissions.
- Monitor and Audit IAM Activity
Use AWS CloudTrail to log and monitor all IAM-related activities. Regularly review these logs to identify any unusual or unauthorized actions. Implementing Amazon GuardDuty can help you detect and respond to potential security threats by continuously analyzing the log data.
- Use IAM Roles for EC2 Instances
Instead of embedding access keys within your applications, use IAM roles to grant temporary permissions to your Amazon EC2 instances. This eliminates the need to manage access keys manually and reduces the risk of accidental exposure.
- Segregate Duties with IAM Groups and Roles
Create IAM groups to organize users with similar job functions and assign the appropriate permissions to each group. This allows you to manage permissions more efficiently and simplifies access management. Additionally, use IAM roles to delegate specific tasks or access to other AWS services without sharing long-term credentials.
- Utilize Temporary Security Credentials
Use the AWS Security Token Service (STS) to generate temporary security credentials for short-term access to AWS resources. Temporary credentials expire after a specified duration, reducing the risk associated with long-term access keys.
Conclusion
Following these IAM best practices will help you create a more secure and manageable AWS environment. Regularly review and update your IAM policies, monitor activity, and implement additional security measures like MFA and access key rotation. By doing so, you can minimize the risks associated with unauthorized access and protect your valuable AWS resources.